
Don’t Let Your IT Partner Turn Into a TV Repairman
Is your IT partner lugging around a bag of tools and fixing things that should have been replaced years ago? I know I am officially
Learn more about what we do and how we help companies just like yours!

Is your IT partner lugging around a bag of tools and fixing things that should have been replaced years ago? I know I am officially

HealthSafeIT is proud to offer top-tier Birmingham IT support designed to meet the unique challenges and requirements of healthcare providers in Birmingham, Alabama. We bring

As a week has passed and the sun has set on the Alabama HLA Summer Conference ended and here are a few observations: Thank you

We’d like to give a warm welcome to one of our newest team members of Stringfellow Technology Group: Jesse Sanders! Jesse will be helping solve
Thank you David from Dothan, Alabama for your feedback: ‘From the beginning he was confident to know my problem and solve my problem perfectly and

When healthcare leaders look for medical managed services, they usually have a lot of questions. Whether it’s about security, efficiency, or cost, they want to

In healthcare and healthcare technology, choosing the best healthcare IT support is crucial for ensuring efficient operations and superior patient care. While much attention is

Many healthcare groups operate under the assumption that local managed services providers (MSPs) are inherently better due to their physical proximity. However, this belief overlooks
In today’s world, technology is the backbone of our daily lives and business operations. From the moment we wake up to the time we go

In the world of healthcare, one principle stands out above all others: “It’s all about the patients.” At HealthSafeIT, we understand the connection between healthcare
Today we’ll explore a critical decision facing many healthcare organizations: choosing between traditional IT personnel and comprehensively managed IT services. As technology becomes increasingly integral

Healthcare providers face unique challenges, from maintaining patient confidentiality to ensuring the smooth operation of complex medical systems. With HealthSafeIT, we understand these challenges and

Finding the right healthcare IT partner is important, but you’ve got to know which questions to ask. To make it easier, we’ve compiled 10 questions

Healthcare Managed Services refers to outsourcing specific IT functions and responsibilities to a third-party provider, such as HealthSafeIT. These technology services are designed to support
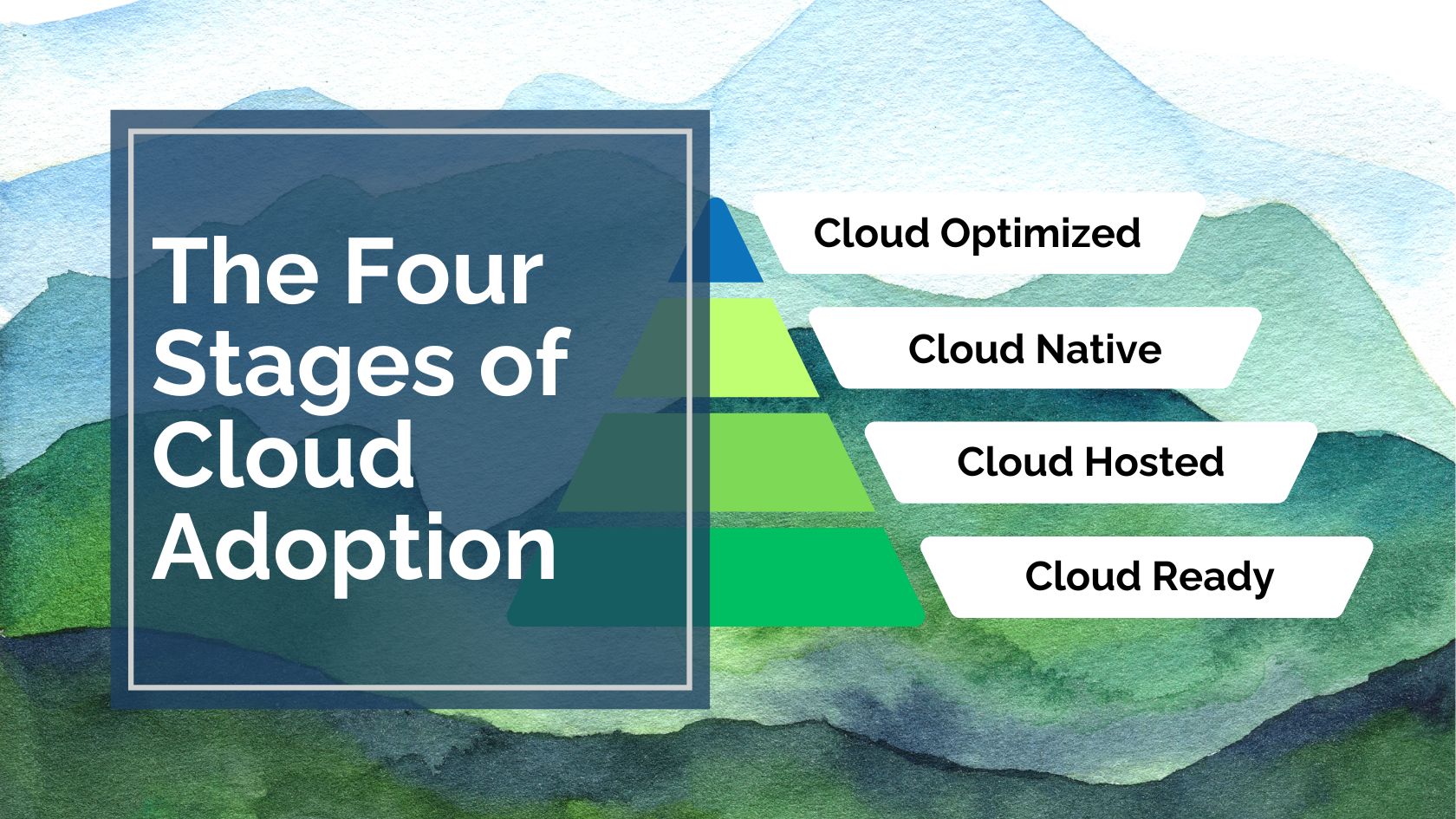
ProSafeIT’s approach to managed technology delivers superior outcomes by taking traditional on-site systems and moving them to the cloud. Your journey through cloud transformation is
But don’t take our word for it. We just got feedback from a client in Austin, Texas who said, “Thanks so much for all your

We get feedback all the time, but it feels good to go above and beyond client expectations and deliver a solution they love. Sarah in

Service Overview: HealthSafeIT’s Remote Support service is designed to provide immediate assistance to end-users, ensuring that technology issues are resolved quickly and efficiently. Our Service
Service Overview: HealthSafeIT’s Managed Network and WiFi services provide your clinic with a robust and secure network infrastructure designed to support all aspects of healthcare
Service Overview: Our Annual Roadmap and Budget service with HealthSafeIT is designed to assist healthcare leaders in making strategic technology investments. By planning your IT

Service Overview: HealthSafeIT provides comprehensive HIPAA Compliant Security and Training services, ensuring that your clinic meets and exceeds the stringent regulatory requirements for safeguarding patient

Service Overview: HealthSafeIT provides specialized Microsoft 365 License and Management services designed to optimize your clinic’s use of this essential suite of productivity tools. With

Service Overview: HealthSafeIT’s Project Planning and Delivery service manages the entire lifecycle of IT projects for your clinic, from initial conception to successful implementation. We

Service Overview: HealthSafeIT’s Dedicated Technology Advisor service offers personalized support and expert guidance tailored specifically to your clinic’s needs. With a go-to expert dedicated to
Service Overview: HealthSafeIT’s User Management service simplifies the complexity of managing clinic staff’s IT needs through seamless user provisioning and management. Our system is designed

Service Overview: HealthSafeIT offers a streamlined approach to Purchasing and Equipment Tracking, simplifying the complexities of IT procurement and asset management for your clinic. Our

In today’s competitive landscape, customer support is not just a helpful tool but a vital component of business success. This is particularly true in sectors

As the industry evolves, small medical practices face healthcare IT challenges that can significantly impact operational costs. Understanding these challenges is crucial for effectively managing

I recently attended the Tennessee MGMA (Medical Group Management Association) conference in Franklin, Tennessee to connect with healthcare administrators on the latest industry trends and
Thank you for the feedback, Heather, in Orlando, Florida! HealthSafeIT helps companies throughout the Southeast United States, including central and southern Florida, find IT service

Welcome to HealthSafeIT. In this blog post, we’ll guide you through the efficient and structured HealthSafeIT onboarding client journey to ensure your business IT needs

Many businesses today rely on new technology to enhance productivity, facilitate efficient communication with clients, and ensure steady growth. At the same time, customers and

With the widespread implementation of the Internet of Things (IoT) in healthcare, security concerns that were previously not considered have suddenly become a reality. In

Electronic medical records (EMRs) allow healthcare providers to keep patients’ health records in digital format, eliminating the need for paper charts and ensuring that clients

If your business handles protected health information (PHI), it’s your duty to take every step possible to ensure that your clients’ data is secured. Cybercriminals

Business intelligence (BI) refers to the process of gathering data and turning it into useful insights. This data can be used to make better decisions

The Health Insurance Portability and Accountability Act of 1996 (HIPAA) was established with the goal of protecting the privacy of medical providers and their patients.

Commuting to work and walking around the office to talk to coworkers helps burn calories throughout the day. But when you’re working from home, the

Perhaps you’ve heard about blockchain, a cutting-edge technology that experts believe has the potential to revolutionize the healthcare industry. But what exactly is blockchain, and

Today’s threats change too quickly for ant-virus products to keep up. By the time a virus is added to the “bad” list on your computer

Many MSPs are struggling to keep up with the security needs of their customers. The volume of incidents, cost of implementing security solutions, and a

The bad guys are real, especially on the Internet. In fact, the bad guys of the Internet are worse than those in real life. At

Business managers continue to want to justify getting all the “good” out of their capital equipment purchases. Computer equipment should no longer be put in

The saying, “common sense is not so common” applies to IT security more than we would like to admit. We all have our areas of

The idea of people actually setting money on fire is pretty humorous. Watching it happen in real life is less satisfying, wasteful even, so let’s

Stringfellow Technology Group, based in Nashville, TN, has acquired CTC Networks based in Franklin, TN. CTC Networks was founded in 1993 and provides managed technology
Email was not designed with security as a requirement. In fact, all “security” that involves email was bolted on after the fact. Here are four
Imagine driving without lines on the road, speed limits, or the need to have a license. Now you know what using email for business communication
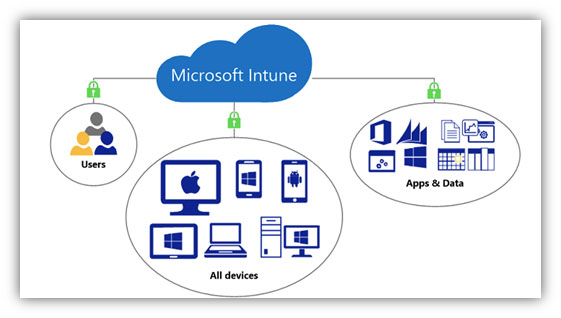
The remote work shift puts the management of devices, applications, and data front and center in the M365 security discussion. The firewall, local Active Directory,

Collaboration is the act of working with someone to produce or create something. In today’s workplace the words “in real time” need to be added
We work best with growing firms who want proactive, executive-level IT strategy, not just help desk tickets.
If that’s you, we’d love to talk.
What You’ll Get From The Conversation:

With over 25 years of business technology experience, Glenn leads our efforts in delivering reliable IT to growing businesses looking to achieve success.
With over 25 years of growing and leading businesses, Jay understands firsthand the challenges leaders face and strive for resolution and growth.