Cyber Insurance for Healthcare: 5 Ways We Help Keep Your HIPAA House in Order

As a healthcare organization, keeping your “HIPAA house” in order isn’t just about compliance—it’s about protecting your patients, reputation, and bottom line. With the rise of cyber threats, compliance alone won’t protect you from financial risks. This is why cyber insurance for healthcare has become essential for small practices. But here’s the kicker: If your […]
Proactive IT Management: The 5 Best Ways to Build a Smarter Future
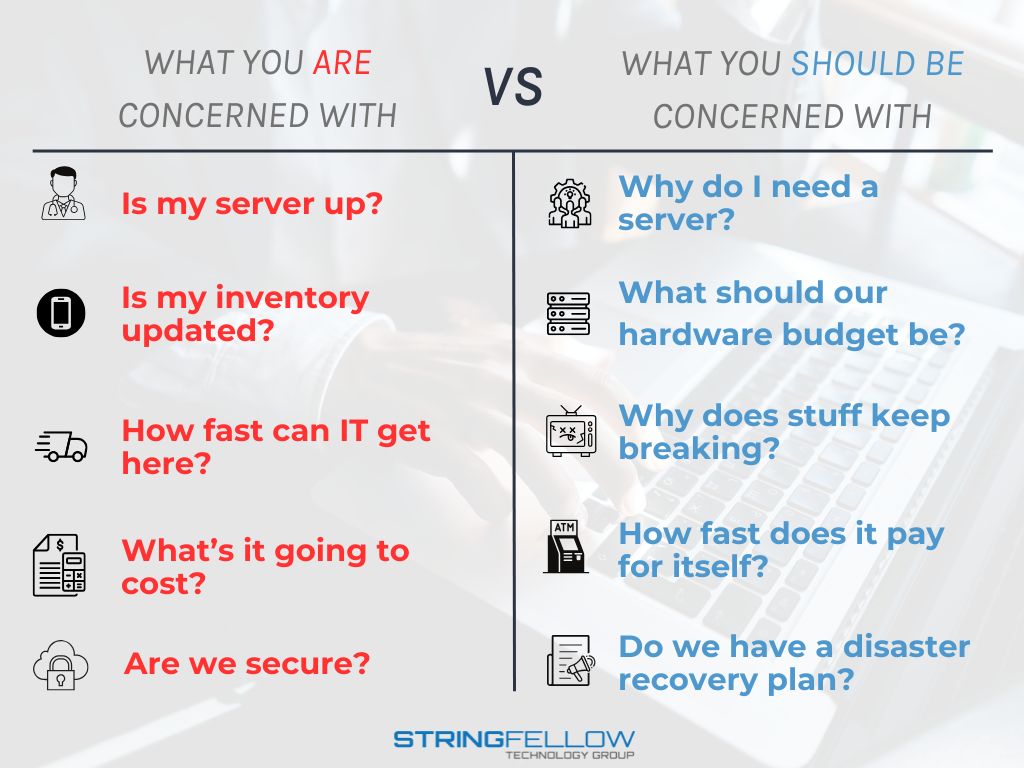
Proactive IT management is no longer a luxury; it’s a necessity for healthcare clinics and growing businesses. As organizations become increasingly dependent on technology, the ability to shift from reactive problem-solving to proactive IT strategies can be the difference between frustration and success. At Stringfellow Technology Group, we specialize in managed IT services designed to […]
Cutting-edge strategies for cybersecurity success

Although cyberattacks on businesses have become increasingly prevalent in recent years, many small-business owners assume that their business is immune to such attacks. This belief often stems from the notion that cybercriminals target larger companies. However, the reality is that cyberattacks are opportunistic crimes, and small businesses often hold a wealth of sensitive data without […]
6 Proven strategies to keep your work devices secure
The rise of remote work and virtual communication has made it more important than ever to secure our devices against cyberthreats. Hackers are constantly finding new ways to exploit our digital vulnerabilities, from webcam spying to unauthorized screen viewing. But don’t worry! There are steps you can take to protect yourself. Install anti-malware software No […]
Before buying antivirus software, consider these factors

With current threats such as viruses, ransomware, and spyware becoming more frequent than ever before, it is essential to have an effective antivirus program installed on your computer. When looking for the right one, however, there are some factors you should take into account. Cost While there are free antivirus programs out there, more often […]
Don’t let ransomware ruin your Mac

If you’re a Mac user, it’s important to be aware of the growing number of ransomware attacks that are specifically targeting macOS devices. Just like Windows users, you need to take precautions to protect yourself from these threats. Here’s how you can secure your Mac against ransomware attacks. Defining ransomware Ransomware is a type of […]
The crucial role of identity and access management in cybersecurity

When it comes to protecting your business from cyberattacks, you can never be too careful. Hackers are always looking for any opportunity to steal critical data or wreak havoc on company systems. To truly secure your business from cyberattacks, you need a comprehensive identity and access management (IAM) solution. IAM: An overview IAM is a […]
Protect your business printers from cyberattacks
Protecting your business printers from malicious cyberattacks may be the last thing on your mind, but it should definitely not be. Hackers are always looking for new vulnerabilities to exploit, and, if left unprotected, printer systems can offer a trouble-free gateway into vast troves of sensitive data. To help safeguard against unforeseen risks, take these […]
Cybersecurity trends that will shape the future of business

Businesses of all sizes can fall prey to cyberattacks that can cause major financial losses and even put companies out of business. And with more numerous and sophisticated threats like these expected in 2023, it’s more critical than ever for business owners to stay ahead of the latest cybersecurity trends and protect their organization from […]
How to Protect Yourself from Internet Hoaxes 101

Cybersecurity is a fast-changing, stressful, and downright scary space to play in. The number and sophistication of cyberattacks are on the rise as hackers continue to outsmart preventive security measures and seep into our environments. It’s becoming evident that navigating how to protect yourself from internet hoaxes and cyber crimes is more challenging than it […]
Improve internet security with VPN

Even if you’re using a firewall and anti-malware software, hackers could still intercept data being sent to and from your device. So if you’re not using a virtual private network (VPN) to browse the internet, you’re leaving your business at risk of data theft. What is a VPN? A VPN creates an encrypted tunnel between […]
How to implement proactive cybersecurity in your business

Businesses today are under constant attack from cybercriminals. In order to protect their data and operations, companies must put in place robust cybersecurity measures such as proactive cybersecurity. This blog post will explain what proactive cybersecurity is and how you can implement it in your business. Benefits of proactive cybersecurity Proactive cybersecurity is a strategic […]
Keeping your firmware up to date

Technology evolves quickly. The features of a phone that came out two years ago are likely very different from the features of the most recent model. It’s the same with printers, laptops, and other devices in your office — newer models with better features are introduced to the market yearly, so you need to keep […]
A guide to IT security terms everyone should know

You’ve probably heard the term “malware” thrown around a lot, but what does it actually mean? In this article, we will define malware and a few other commonly used terms in IT so you can better protect your business. Understanding these basic cybersecurity concepts doesn’t require deep IT expertise, so read on. Malware For a […]
Securing Microsoft Teams: Practical tips to keep your workplace safe
Microsoft Teams is a great tool that can help improve communication and collaboration in the workplace. However, the popular business communication platform can also be a security concern if it’s not adequately secured. In this blog, we’ll dive into some practical tips for securing Microsoft Teams and keeping your workplace safe. Utilize built-in security features […]
Protecting your Microsoft 365 environment and data

For many businesses, Microsoft 365 is their go-to productivity suite because it offers powerful features, cost-saving benefits, and world-class security. And while Microsoft continuously looks for ways to address security concerns, the changing threat landscape can put Microsoft 365’s security measures to the test. Here are some of the most common security risks Microsoft 365 […]
The three kinds of hackers every business should watch out for

Hackers come from all different backgrounds. Some hackers are motivated by money and politics, while others simply hack systems for fun. In this blog post, we will define the three kinds of hackers and how each one differs from the others. A complicated history In the 1950s, the term “hacker” was vaguely defined as someone […]
Five Ways Your Team Can Boost Productivity with Azure AD

Everyone wants a more productive team, but with Azure AD you can deliver a lot of time saving benefits without much additional cost or another server. You may not recognize Azure AD as something you use, but if you use Microsoft 365, you’re already in Azure and you’re already using Azure AD. Azure AD is […]
The crucial role of MSPs in SMB cybersecurity

With modern cyberattacks targeting companies of all sizes, businesses cannot afford to relegate cybersecurity to the bottom of their list of priorities. When it comes to cybersecurity, even small- and mid-sized businesses (SMBs) would do well to get help from an expert. Here’s how having a managed IT services provider (MSP) implement robust cybersecurity solutions […]
Fileless malware: The invisible threat

Hackers have found a clever way to get around anti-malware software — they’re using fileless malware, a type of malicious software that’s not as visible as traditional malware. This means it can infect your entire infrastructure without you even knowing. Let’s take a closer look at how fileless malware works and what you can do […]
The risks of password autofill
Hackers may have found an effective way to track users using a web browser or password manager’s password autofill feature. Here’s how they do it and what you can do to protect yourself. Why password autofill is so dangerous Modern web browsers and password managers have a feature that enables usernames and passwords to be […]
TPM 2.0: Why bypassing it is risky for your business

Microsoft requires devices to carry a Trusted Platform Module (TPM) 2.0 chip in order to meet Windows 11’s minimum hardware requirements. If your business uses computers that are two or three years old, then those machines likely don’t have this chip. That means you may have to invest in new devices just to run Windows […]
Keep cybercriminals from attacking your business printers with these tips

It’s easy to overlook printers when implementing a cybersecurity strategy, as they may seem safe from cyberattacks. But in reality, many hackers these days exploit certain printer vulnerabilities to gather information about businesses or even infiltrate their systems without anyone noticing. Protect your business printers by following these tips. What makes business printers vulnerable to […]
Surf securely with a VPN
There was a time when installing an antivirus program was enough to secure your data, but that’s no longer the case today. Whether you want to keep your online activities hidden from third parties or prevent your data from being intercepted by hackers, you need to invest in a virtual private network (VPN). What is […]
What is proactive cybersecurity, and how do you implement it?

To keep cyberthreats at bay, you need proactive cybersecurity solutions in your arsenal. They identify and contain threats before they wreak havoc on your systems and cause significant productivity and financial losses. Here’s all you need to know about proactive cybersecurity and how to implement it. What is proactive cybersecurity? Traditional cybersecurity is reactive — […]
Are your company mobile devices protected?

Mobile devices are indispensable. Smartphones, tablets, and other mobile gadgets play a big part in everyday processes, especially for individuals and companies that value connection and convenience. But as the number of mobile devices used in business operations increases, so do the cyberthreats that target them. Be sure to follow these steps to safeguard company […]
How updated firmware keeps cyberattacks at bay
Your business may have all the latest cybersecurity solutions in place, but if you haven’t updated your computers’ firmware in a while, you may still be at risk of data breaches and other cyberattacks. Here’s how updating firmware can beef up your company’s cyber defenses. What is firmware? Firmware is a basic type of software […]
Shopping for antivirus software? Consider the following points

As viruses, ransomware, and spyware become more dangerous these days, it’s more important than ever to have powerful antivirus protection. When choosing the right antivirus program for your computer, however, there are many things you should consider. Let’s take a look at the most important ones. Cost There are free antivirus programs in the market, […]
3 Simple tips for thwarting cybercriminals

Advances in technology have made life easier but have also enabled cybercriminals to improve their techniques. This can be a big blow to small-business owners who often take data security for granted. To keep your business safe, follow these simple tips. Cover your webcam If Facebook founder Mark Zuckerberg, former FBI Director James Comey, and […]
Basic cybersecurity terms everyone should know

If the only cybersecurity terms you know are “virus” and “hacking,” now is the time to expand your cybersecurity vocabulary. This will enable you to better understand the variety of risks in the online world and protect your computers, data, and yourself. Here’s a short yet handy list of cybersecurity terms you should know. Malware […]
How to mitigate Microsoft 365 security risks

Microsoft 365 has transformed the way many organizations work by enhancing workflows, collaboration, and efficiency. But like other cloud-based solutions, this line of subscription services is not immune to security risks. Here’s what your business can do to address these challenges. Vulnerabilities in SharePoint Businesses typically use SharePoint Online and on-premises SharePoint sites to store […]
If you’re experiencing a ransomware attack, try these online decryptors

While the threat of ransomware pretty much encompasses all of cyberspace nowadays, not everyone realizes that some ransomware threat responses are readily available for anyone who might need them. Take a gander at these decryptor websites, for instance. They may come in handy sometime. The state of ransomware in 2021 so far Businesses need to […]
Small- and mid-sized businesses need cybersecurity

If your company has recently suffered from a data breach or a ransomware attack, then you know how costly it can be. You lose not just hundreds of dollars but also the reputation you’ve built through the years. That’s why you need cutting-edge cybersecurity solutions to protect your business from ever-growing cybersecurity threats. The good […]
Everyone’s role to play in proactive cybersecurity

As IT security consultants and managed service providers, we are business partners who provide clients with enterprise-level IT. We specialize in overwhelmingly intricate technology and keep ourselves abreast of the latest cybersecurity developments. However, as with all partnerships, you have a role to play, too. Here’s how you and everyone in your team can play […]
How to pick a VPN for your business

A virtual private network (VPN) offers a host of security and privacy benefits, especially if you’re surfing the web or transacting online over a public Wi-Fi network. A VPN ensures that your online activities are always secure and private. So what factors do you need to consider when selecting a VPN, and how do you […]
Obsolete firmware poses security risks
Are you still hanging on to your old work computers since they “still work fine”? While they may still help you get the job done, their outdated firmware can make you vulnerable to security risks that can lead to major problems. What is firmware? Firmware is a basic type of software that is embedded into […]
A closer look at fileless malware

To avoid detection by anti-malware programs, cybercriminals are increasingly abusing legitimate software tools and programs installed on computers to initiate attacks. They use fileless malware to infiltrate trusted applications and issue executables that blend in with normal network traffic, IT processes, and system administration tasks while leaving fewer footprints. Ultimately, your business could be at […]
Keep your mobile devices safe with these tips

Mobile devices are generally less secure than laptop and desktop computers. While there are available anti-malware applications for smartphones and tablets, they aren’t as comprehensive as those for laptops and desktops. Additionally, some mobile devices aren’t compatible with certain security applications or measures implemented by businesses. That’s why it’s even more important to keep track […]
Diving into Data Backup

Data loss is something we all know happens but many don’t like to talk about. We all assume it won’t happen to us if we just look after our devices but the reality is that it could happen to anyone, at any time. Whether hacking takes place or we accidentally damage our devices there’s a […]
New Android malware detected!

If you have an Android device, be careful! An exceptionally dangerous Android malware known as DEFENSOR ID is currently making the rounds in the Google Play Store. The malware exploits the Accessibility Services in an Android device to evade detection by traditional security measures. This threat can put your data and business in jeopardy, so […]
Are your business printers protected against hacks?
When it comes to cybersecurity, you probably think of protecting computers, apps, or online databases first and printers last. Precisely because they’re overlooked in, printers can be exploited by hackers and used as a gateway to infiltrate your systems. Secure your networks against intruders by following these steps. What makes business printers vulnerable to cyberattacks? […]
Another Windows 10 update, another raft of issues
It’s the update season for Windows 10 users. Although it’s normal for us to experience an uptick in support requests during these periods, things are looking worse than normal this time around. That’s because Microsoft’s most recent operating system update has caused data loss for some users. Let’s discuss how you can prevent this from […]
Keep these in mind when shopping for antivirus software

If you think cybersecurity is only for big organizations, think again. Small- and mid-sized businesses often don’t have the budget for expensive cybersecurity tools, making them easier targets for cybercriminals. Statistics show that cybercrimes continue to increase every year. And with the global pandemic forcing businesses to work from home, protection from cyberthreats such as […]
Security best practices for remote workers

Working from home increases employee autonomy, cuts costs, and ensures the health and safety of the company during the coronavirus pandemic. The problem is, it also increases the likelihood of security breaches since employees are working outside the company’s security perimeter. That’s why you and your staff must adhere to these security best practices. Fortify […]
Autocomplete password risks

Web browsers come with features to improve user experience. One of the most popular ones is auto-fill passwords. These are designed for users to store and automatically use their account credentials to access websites and other applications. While auto-fill passwords are convenient, they come with security risks. Read more. Why auto-fill passwords are so dangerous […]
3 Hats a hacker might wear

While not always accurate in its portrayal of hackers, Hollywood does get at least one thing right: there are many types of hackers out there, all with varied methods and motivations. In this article, we’ll take a look at three main types of hackers. A complicated history In the 1950s, the term “hacker” was vaguely […]
Office 365 hacking: What you need to know

Some hackers have become so skilled that they don’t even need you to give up your credentials to hack into your account. One recent cyberthreat is targeted towards users of Microsoft Office 365. You don’t want to be the next victim, so read up. A phishing scam that harvests users’ credentials The latest cyberattack on […]
Data security: Prevent insider threats

In the healthcare industry, 58% of security incidents begin with an inappropriate action carried out by someone within the affected organization. Although the percentage isn’t as high among other industries, it’s still something you can’t afford to ignore. Here’s a look at five ways to prevent such breaches. #1 Educate You must teach your team […]
This malware can easily slip through Windows 10 security

Sophos researchers are warning Windows 10 users about a new type of malware that can disable and bypass computers’ security software. Known as Snatch, this ransomware is comprised of a collection of tools, including a separate data stealer. Designed to target businesses, this ransomware forces your Windows PC to reboot in Safe Mode to prevent […]
The benefits of hyperconverged infrastructure

Hyperconvergence isn’t something only large enterprises can benefit from — businesses of all sizes should consider this infrastructure strategy. Read on to learn more about what hyperconvergence can do for your company. What are hyperconverged infrastructures? In a traditional IT environment, networking, server, and storage hardware need to be purchased separately and configured to work […]